Cybersecurity consistently ranks as a key priority and challenge for human services agencies. Now that remote work and telework are here to stay, it’s increasingly important for agencies to provide caseworkers with technology that’s safe, secure, and easy to access from anywhere without increasing vulnerability. We’ve rounded up resources to help you keep cybersecurity at the forefront of your IT planning and purchasing.
Full summary:
“The pandemic may have paused many activities, but it didn’t slow down the growth of cyber threats. In fact, 61 percent of the local governments surveyed said they saw an increase in cyber threats during 2020. Not a single respondent said that cyber threats decreased.” – The Center for Digital Government
A recent cybersecurity survey from the Center for Digital Government provides several data points that underscore why cybersecurity has regained so much attention within the last year:
- While 61% of respondents said they saw an increase in cyber threats, 69% still lack confidence in their organization’s ability to respond
- Continued use of aging technology is the top reason for respondents’ low confidence levels
- The top three types of cyber threats all relate to the actions of people: human error, social engineering, and compromised accounts and user credentials
- More than 90% of participants recognize that cloud technology plays an increasingly important role in an organization’s cyber response strategy
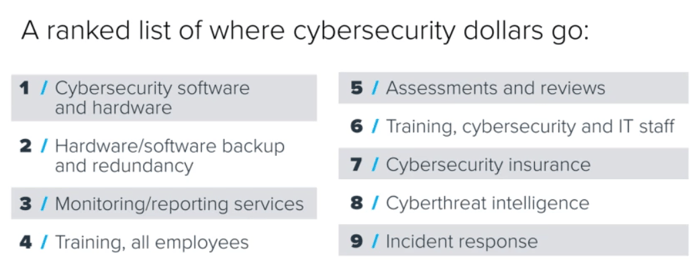
Recognizing that risks abound, agencies prioritize investing in cybersecurity software and hardware, followed by hardware/software backup and redundancy, monitoring/reporting services, and training.
 Source: GovTech Navigator Market Facts
Source: GovTech Navigator Market Facts
While all these investments are clearly important, agencies with limited IT resources may inadvertently overlook another critical element because they’re already balancing so many priorities. They need to ensure that all technology provided to caseworkers is safe, secure, and easy to access from anywhere without increasing vulnerability.
As noted in GovTech’s article, an overnight shift to remote at the beginning of the COVID-19 pandemic exacerbated this challenge because agencies had to move so quickly:
“When employees worked all within the same physical confines, there was a boundary around them, so the organization could fend off attacks. Now the boundary is in lots of people’s homes. It is a different technical issue.” – John Gilligan, president and CEO, Center for Internet Security
“The danger would be that in the urgency of the moment, a lot of these security controls would be put on a checklist to get back to, but IT teams would feel they don’t have time to do it right now. They are just going to open up these ports and protocols to allow people to work.” – Mark Weatherford, chief strategy officer, National Cybersecurity Center
Key Security Questions When Evaluating Software
To mitigate this risk, here are some security-related questions we recommend asking vendors before you purchase or provide caseworkers with any new tools:
- How is your software application monitored?
- How do you authenticate user login information?
- Does the solution require complex passwords?
- Does it terminate session upon timeout?
- Where will our data be stored?
- How will our data encrypted? Will it be encrypted during transit and at rest?
- How does your solution integrate with other technologies?
- What are your backup and restore procedures?
- What other safety and privacy measures are built in?
- How often do you audit your security/privacy audits and controls?
- What is your uptime SLA (service level agreement)?
 Cybersecurity Resources for Human Services
Cybersecurity Resources for Human Services
If you want to learn more about how Northwoods safeguards our clients and their data, please don’t hesitate to reach out. In the meantime, bookmark these resources for more cybersecurity strategies, best practices, and tips.
- Cybersecurity Handbook: Tips and Tricks to Stay Safe [GovLoop] – learn key definitions, best practices, and answers to critical cybersecurity questions.
- Stronger Together: State and Local Cybersecurity Collaboration [NASCIO] – outlines promising programs that states have initiated to enhance collaboration with their local government counterparts.
- Technology and Telecommunication Priorities Focus on Cybersecurity [NACo] – shares insights from a conference panel discussing ways to improve cybersecurity at the local level. (This brief provides additional information on cybersecurity priorities and best practices for counties from NACO's Telecommunication and Technology Policy Steering Committee.)
- Cybersecurity is YOUR Responsibility [NASPO] – summarizes what’s at stake if government infrastructure gets compromised and offers cyber defense tips specific to state and local government employees.
- 6 Cybersecurity Tips When You Work from Home [Forbes] – tips to help remote workers protect themselves.
- 7 Questions to Help Evaluate the Strength of Your Cybersecurity Program [Plante Moran] – poses seven questions you should ask yourself to build a strong, risk-focused security culture within your organization.
- Regulated Industries and Agencies Compliance Checklist [SecureLink] – designed to assist organizations with an initial security audit and to identify problems or gaps in security policies.